All the sessions from Transform 2021 are accessible on-demand now. Watch now.
Ninety-seven % of cloud-native safety practitioners are broadly unaware of crucial container safety principles, according to a report from Aqua Security.
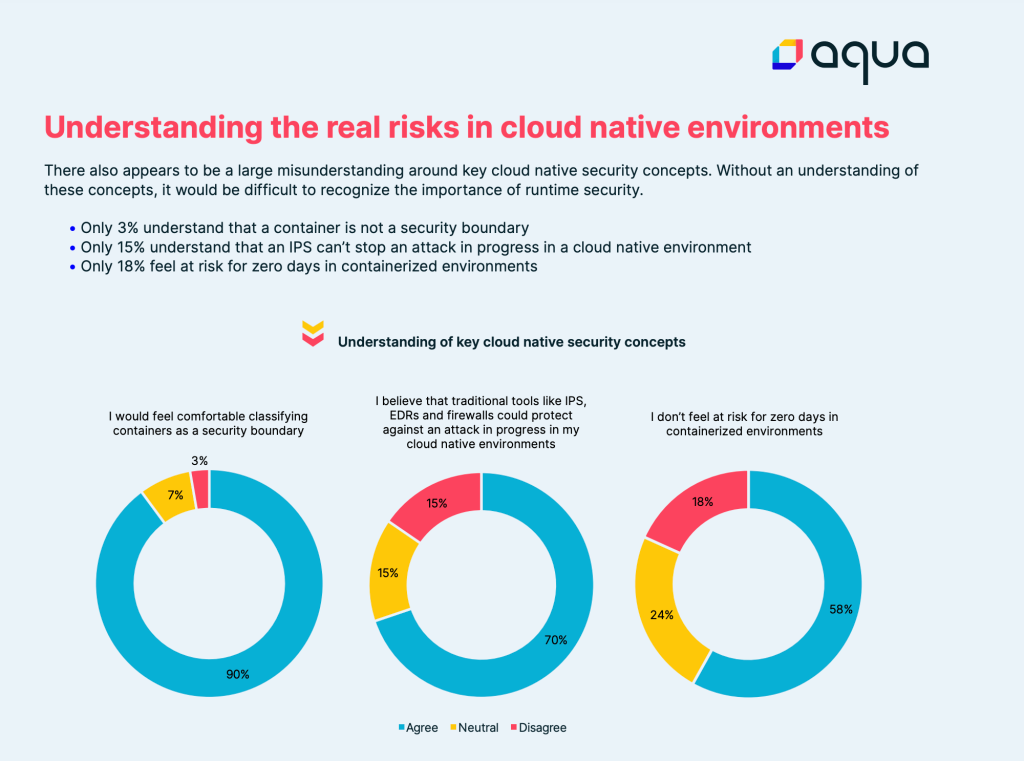
Just 3% of respondents appropriately noted that a container is not a safety boundary. This discovering, combined with the reality that 70% believed classic tools — such as an IPS or firewall — could guard against attacks in progress in a cloud-native atmosphere, highlights the difficulty and complexity of understanding important cloud-native safety dangers and how to counteract them.
A complete 58% did not really feel at threat for zero days in containerized environments, and safety researchers have located attackers are becoming increasingly sophisticated more than time. Fifty % of vulnerable targets are getting attacked inside the hour. And even though 73% of respondents have been confident in their potential to quit application provide chain attacks, only 32% have been confident in the runtime capabilities expected to quit threats like Kinsing malware, which only downloads in runtime.
Practitioners did not report robust plans to invest in runtime as a important element of a complete lifecycle cloud-native safety method. Runtime safety is essential in guarding against attackers evading static evaluation or otherwise receiving about more well-known, and far better understood, shift-left controls. While static evaluation plays an significant function in container safety, it is by no indicates a silver bullet. Even the most total shift-left vulnerability and malware detection can’t protect against zero-day attacks and administrator errors.
Despite the extensively publicized threat landscape, only 24% of respondents claimed they planned to introduce runtime controls in the coming year, even though significantly less than 16% have been in reality organizing on investing in the essential creating blocks of runtime safety (for instance, making certain container immutability). These investment plans have been reported in spite of the reality that only 26% of respondents stated 70% or more of their cloud-native safety stack could quit an attack in progress in a cloud-native atmosphere.
The study interviewed 150 practitioners across industries ranging from economic services to the public sector. The cohort of practitioners interviewed all worked for big organizations, with headcounts ranging from 1,000 to more than 10,000. Forty-seven % had at least 5 years of cloud-native safety company practical experience.
View the complete Aqua Security 2021 Cloud Native Security report.