The pandemic didn’t slow targeted cyberattacks by criminals and nation-states, according to the 2021 Global Threat Report by cybersecurity firm CrowdStrike. The firm predicts that adversaries in 2021 will be as prolific as ever.
CrowdStrike mentioned that for the duration of COVID-19 it saw a lot more “big game hunting,” exactly where criminal organizations turned to stealing information from massive institutions such as hospitals and then held that information for ransom. The most disturbing point about the report is that it describes a entire criminal ecosystem headed by big organizations, rather than just a collection of person and opportunistic attacks.
A total of 104 wellness care organizations have been targeted with attacks from 18 distinctive parties in 2020, and the market will continue to face an onslaught of ransomware attacks, risking disruption to important care facilities. CrowdStrike mentioned that worry, concern, and curiosity surrounding COVID-19 offered the ideal cover for a record-setting raise in social engineering attacks from each eCrime actors and targeted intrusion adversaries. One group dubbed Twisted Spider was accountable for 26 attacks on wellness care organizations.
“The allure of big game hunting (BGH), ransomware campaigns aimed at high-value targets, dominated the ecosystem of eCrime enablers in 2020, spurring the market for network access brokers,” the report mentioned. “BGH trends also disrupted traditional targeted eCrime behavior — as seen by threat actor Carbon Spider’s shift away from the targeting point-of-sale (POS) systems to join the BGH ranks.”
China and North Korea

Image Credit: CrowdStrike
As such, the COVID-19 vaccine will be a main target for many China-based and North Korean adversaries. Economic espionage from these adversaries is predicted to raise in 2021, with a specific concentrate on entities involved in the study, production, or distribution of COVID-19 therapeutics, in addition to technologies in the agriculture sector.
North Korea is anticipated to be especially motivated, in component by way of its want to acquire sources and currency to deal with a meals shortage associated to the pandemic. The blending of eCrime and targeted intrusion techniques previously linked with these North Korean actors and some Russian adversaries was also observed in an Iran-focused group dubbed Pioneer Kitten.
China’s cybersecurity hackers will concentrate on provide chain compromises and the targeting of important Western verticals when it comes to COVID-19 vaccines, as effectively as targets in academic, wellness care, technologies, manufacturing, and aerospace. Chinese adversaries targeted telecommunications, with a group dubbed Wicked Panda possessing one more prolific year, regardless of indictments against men and women linked with their operations.
In July 2020, the U.S. Department of Justice (DOJ) indicted two Chinese nationals with alleged ties to the Chinese Ministry of State Security (MSS) for wide-ranging cyber operations, the most current of which reportedly integrated targeting U.S.-based COVID-19 study centers. Intelligence officials in Spain also claimed that a China-nexus actor had effectively stolen facts relating to COVID-19 vaccine improvement from Spanish study institutes in September 2020. In addition to this reported activity, CrowdStrike identified 5 suspected China-origin campaigns targeting wellness care entities in 2020.
Russia was also active. In July 2020, the U.S., U.K., and Canadian governments released facts describing a campaign from a group dubbed Cozy Bear that targeted COVID-19 study facilities. This campaign was reportedly carried out all through 2020 and was most likely intended to steal facts relating to the improvement and testing of vaccines targeting the virus. CrowdStrike also identified the rise of Latin American hacking groups, with malware households that involve Culebra Variant, Salve, Caiman, and Kiron.
Supply-chain attacks
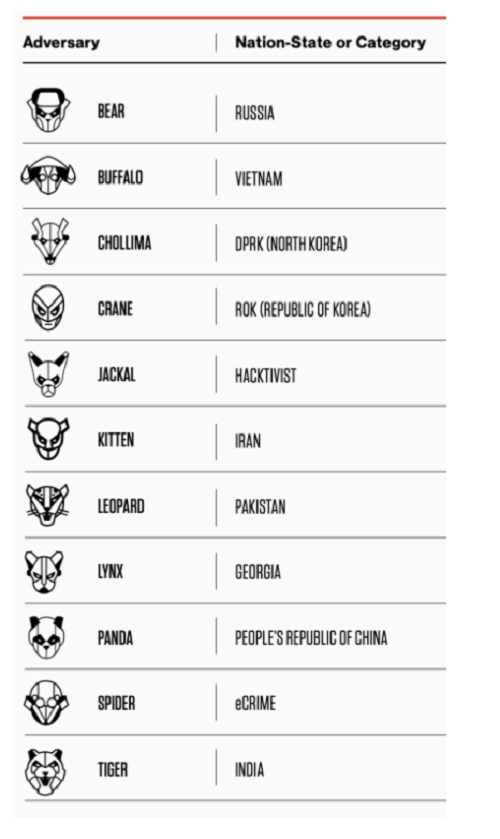
Image Credit: CrowdStrike
The targeting of the provide chain will also amplify in 2021 as cybercriminals seek economic payouts and nation-states use it to deploy espionage-driven tools.
Supply chain attacks are nothing at all new. CrowdStrike publicly raised them as a increasing threat as far back as 2018 and believes they will continue to be a important intrusion vector. Supply chain attacks represent a exceptional initial access tactic that gives malicious actors with the potential to propagate from a single intrusion to many downstream targets of interest. In addition to computer software-based attacks, such as the one that impacted SolarWinds (a suspected Russian spying campaign that broke into nine federal agencies and at least one hundred corporations), provide chain attacks can take the kind of hardware or third-party compromises.
CrowdStrike Intelligence has identified provide chain and trusted partnership compromises originating from each eCrime and targeted intrusion adversaries. eCrime actors frequently use the access from these compromises for economic get, commonly deploying ransomware and mineware, whereas targeted intrusion adversaries mainly use compromises to deploy espionage-driven toolsets to a broad set of customers. Given the prospective higher return on investment for threat actors, CrowdStrike Intelligence anticipates these attacks will continue to threaten organizations across all sectors in 2021.
Sunnyvale, California-based CrowdStrike mentioned its new eCrime index will measure the attacks in weekly updates based on 18 distinctive indicators of criminal activity. Of all the attacks uncovered, CrowdStrike mentioned eCrime accounted for 79%.
A common vector for cybercriminals is the provide chain, as it enables malicious actors to propagate many downstream targets from a single intrusion. Nation-state adversaries also infiltrated networks to steal beneficial information — especially searching for COVID-19 vaccine study — and have accomplished so when evading detection inside the networks for a period of time. CrowdStrike’s Adam Meyers, senior vice president of intelligence, mentioned in a statement that firms and institutions want to deploy cloud-native technologies to avert attacks and get much better visibility across an enterprise.
Extortion is anticipated to continue with the introduction of Dedicated Leak Sites (DLS). In June 2020, following an explosion of devoted leak internet sites in the initial half of the year, Twisted Spider branded itself the leader of Maze Cartel, which was a cooperative work amongst Twisted Spider, Viking Spider, and the operators of LockBit ransomware, as effectively as unconfirmed involvement from the operators of SunCrypt and Wizard Spider. The Maze Cartel shared leaked information from their operations on every of their DLSs, most likely in an work to attain a wider audience, therefore placing more stress on victim firms.
Another component of the ecosystem is access brokers, who get backend access to different organizations (corporations and government entities) and sell this access — either on criminal forums or by way of private channels.
CrowdStrike collects information on attacks through its different items, processing 4 trillion events per week across 176 nations.
Recommendations
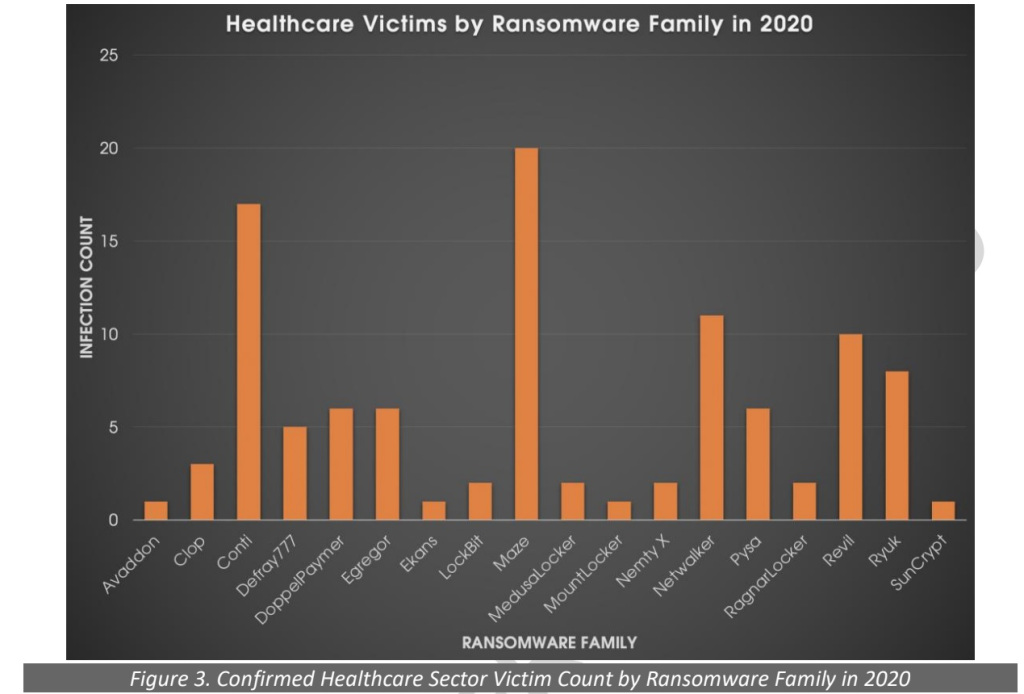
Image Credit: CrowdStrike
CrowdStrike mentioned that as threat actors add new tools, methods, and procedures to their arsenals and kind new alliances to bolster their strength and extend their attain, visibility and speed are more important than ever. Security teams should turn into more versatile, proactive, and productive to remain ahead of threats.
As their operations mature, each eCrime and targeted intrusion adversaries will continue to create and implement new techniques to bypass detection and impede evaluation by researchers, CrowdStrike mentioned. Whether driven by public reporting or motivations internal to their respective organizations, the pursuit of operational safety will virtually undoubtedly involve enhanced obfuscation techniques, use of commodity tooling and living-off-the-land (LOTL) methods.
The challenges of 2020, such as the fast pivot to “work-from-anywhere,” have triggered a level of social and financial upheaval that is unprecedented in contemporary occasions. The widespread influence has not deterred cyber adversaries — in reality, very the opposite. In 2020, CrowdStrike observed adversaries exploiting the scenario, preying on the public’s worry and escalating attacks. CrowdStrike’s suggestions are aimed at proactively addressing prospective weaknesses prior to they can be leveraged by attackers.
For safety teams operating in today’s atmosphere, visibility and speed are important for blocking attackers that have the capability and intent to steal information and disrupt operations. Security teams should have an understanding of that it is their duty to safe their cloud environments, just as they would on-premises systems. They should establish constant visibility for all environments and proactively address prospective vulnerabilities prior to they can be leveraged by attackers, CrowdStrike mentioned.
Organizations should think about multifactor authentication (MFA) on all public-facing employee services and portals as mandatory. In addition to MFA, a robust privilege access management procedure will limit the harm adversaries can do if they get in and lessen the likelihood of
lateral movement.
And CrowdStrike mentioned “Zero Trust” options really should be implemented to compartmentalize and restrict information access, therefore decreasing the prospective damages from unauthorized access to sensitive facts.
