Where does your enterprise stand on the AI adoption curve? Take our AI survey to uncover out.
Gaming faced the highest development in cyberattacks throughout the pandemic, according to a report by Akamai Security Research.
The report showed that “relentless” net application and credential stuffing attacks targeting gamers and gaming businesses persisted all through 2020, stated Steve Ragan, Akamai safety researcher and author of the “State of the Internet Security report,” in an interview with GamesBeat.
Akamai supplies options for safeguarding and delivering digital experiences. Today, it released analysis displaying that cyberattack targeted traffic targeting the video game business grew more than any other business throughout the COVID-19 pandemic.
The report stated the video game business faced more than 240 million net application attacks in 2020, a 340% improve more than 2019.
Mobile gaming attacks preferred
Image Credit: Akamai
Ragan stated that attackers are also going right after mobile gamers.
“People like to play their games on a phone versus having to log into the computer or sit down in front of a TV,” he stated. “But victims in these crimes don’t really think of security. I think of security all day long. But my kids don’t think about security when they’re playing their games.”
Mobile games incorporating in-app purchases are topic to a constant barrage of attacks, according to the Akamai report. Criminals are in search of any chance to exploit players who devote actual dollars on virtual, in-game things like skins, character enhancements and extra levels. The report highlights a current instance in which negative actors made use of a phishing kit to steal player e-mail addresses, passwords, login particulars, and geolocation data that they subsequently sold on criminal markets.
Ragan stated Akamai is observing a persistence in video game business defenses becoming tested on a everyday — and normally hourly — basis by criminals probing for vulnerabilities by means of which to breach servers and expose data. Numerous group chats forming on preferred social networks are devoted to sharing attack tactics and very best practices.
“They started with the credential stuffing testing against every platform and every type of service you can think of including all the gaming ones,” Ragan stated. “They went after Zoom, and then they pivoted, going after other verticals like streaming, media, gaming, and finance.”
SQL injection (SQLi), which targets player login credentials and private data, was the best net application attack vector in 2020, representing 59% of all attacks Akamai observed against the gaming business.
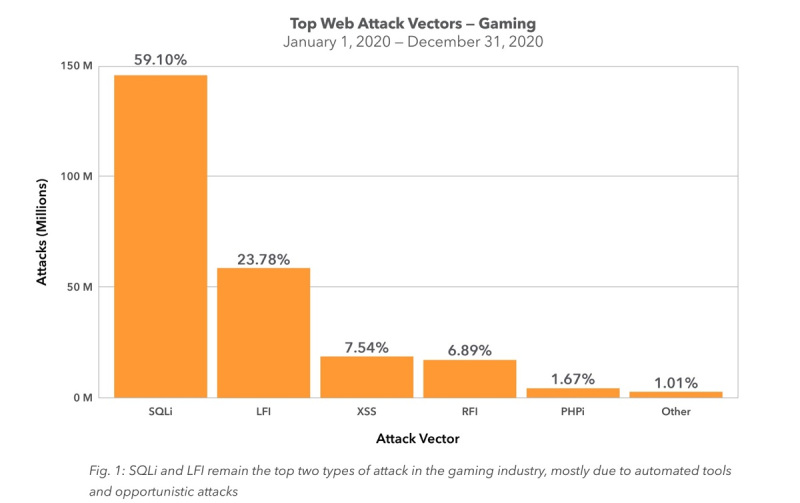
Image Credit: Akamai
That was followed by nearby file inclusion (LFI) attacks at 24%, which target sensitive particulars inside applications and services that can additional compromise game servers and accounts. Cross-web-site scripting (XSS) and remote file inclusion (RFI) attacks accounted for 8% and 7% of observed attacks, respectively.
The video game business suffered almost 11 billion credential stuffing attacks in 2020, marking a 224% improve more than the preceding year. The attacks had been steady and huge, taking spot at a price of millions per day, with two days seeing spikes of more than one hundred million.
“What you’re seeing is the spikes in gaming are correlating to the spikes globally. And consistently throughout the year, you’re looking at millions of attacks a day, spiking in some points to 76 million in the gaming industry in April,” Ragan stated.
Second only to phishing in recognition of account takeover attacks, credential stuffing attacks had been so frequent in 2020 that bulk lists of stolen usernames and passwords had been offered for as tiny as $5 on illicit web sites.
“The market is just flooded with credentials,” Ragan stated.
Ragan stated that customers recycling and employing easy passwords make credential stuffing such a continual challenge and productive tool for criminals. He stated a profitable attack against one account can compromise any other account exactly where the exact same username and password mixture is becoming made use of. Using tools like password managers and opting into multi-aspect authentication wherever feasible can support get rid of recycling and make it far more challenging for negative actors to execute profitable attacks.
“Not only had been they undertaking their regular crime campaigns, credential stuffing, phishing, internet site, exploitation, issues like this,’ Ragan stated. “They had been education every single other, operating classes, sharing informational sources that about the best tactics for undertaking a form of scam.

Image Credit: Akamai
One issue is clear to Ragan.
“It’s not just the gaming companies responsibility or a player’s responsibility,” he stated. Both sides have to equally come to the table when safety matters are addressed.”
Crypto wallets below assault
Cybercriminals have been going right after crypto wallets as effectively.
“Wallet jacking has always been a thing. It’s been around since the early days of crypto in general,” Ragan stated. “But what’s interesting is as the crypto market gains more public visibility, and there’s more money to be had, criminals focus on that.”
Criminals will get the logs that have stolen from a user’s computer after it is been infected with malware.
“What the criminals are doing is they’re paying for the logs that have crypto wallet passwords in them just so they can take the money out of it,” Ragan stated.

